TL;DR:
- Digital identity underpins trust, compliance, and brand growth beyond just login credentials.
- Proper frameworks and risk assessments help manage threats like fraud and biometric attacks.
- Ethical, user-centric identity models like SSI build trust and reduce data liability.
Digital identity is not simply a username and password. For SaaS founders and ethical startups, it is the architecture that underpins trust, compliance, and long-term brand growth. Get it wrong and you face fraud exposure, regulatory penalties, and users who simply walk away. Get it right and you gain a measurable competitive edge. This guide covers what digital identity truly is, how the core frameworks operate, where the real risks lie, and how to use it as a strategic asset rather than a technical afterthought.
Table of Contents
- Defining digital identity: Components and concepts
- How digital identity works: Frameworks and real-world mechanics
- Risk, resilience, and edge cases in digital identity
- The business case: Why digital identity matters for growth and trust
- Adopting and evolving digital identity in your business
- Perspective: What most guides miss about digital identity
- Take your SaaS brand’s digital identity further
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Digital identity scope | It involves authentication, authorisation, and trust—not just logins or passwords. |
| Framework selection | Choosing the right digital identity model balances user privacy, brand needs, and risk. |
| Business growth driver | Strong digital identity systems reduce churn, drive higher ROI, and boost trust. |
| Risk management | Proactively addressing identity risks and inclusion challenges averts costly issues. |
| Implementation steps | Strategic planning, NIST guidelines, and hybrid frameworks help future-proof identity. |
Defining digital identity: Components and concepts
Digital identity refers to the set of attributes used to identify, authenticate, and authorise individuals or entities in digital interactions, managed through processes defined in NIST SP 800-63-4. That definition matters because it immediately signals scope. This is not just about logins. It covers every data point your platform uses to verify who someone is and what they are permitted to do.
The three core processes are identity proofing, authentication, and federation. Proofing establishes that a user is who they claim to be. Authentication verifies that claim each time they access your system. Federation allows trusted identity data to move across platforms without the user needing to re-prove themselves at every step.
Typical digital identity elements include:
- Usernames and passwords (the baseline, and the least secure)
- Passkeys (cryptographic credentials tied to a device)
- Federated credentials (such as signing in via Google or LinkedIn)
- Verifiable credentials (digitally signed documents, like qualifications or licences)
- Biometrics (fingerprints, facial recognition, voice patterns)
Businesses that invest in SaaS digital strategies and build robust identity frameworks see measurable results. Brands with strong digital identity practices report a 27% reduction in churn, because users trust platforms that handle their data with precision and care.
Pro Tip: Before choosing an identity solution, run a NIST-aligned risk assessment. It will tell you which assurance level your use case genuinely requires, saving you from over-engineering or under-protecting your system.
How digital identity works: Frameworks and real-world mechanics
Core mechanics include identity proofing, authentication, and federation to enable secure access across systems. NIST structures these across assurance levels: Identity Assurance Levels (IAL1 to IAL3), Authenticator Assurance Levels (AAL1 to AAL3), and Federation Assurance Levels (FAL1 to FAL3). Higher numbers mean stronger verification and lower risk tolerance.
Beyond the levels, identity methodologies encompass centralised, federated, user-centric, and self-sovereign identity (SSI), with SSI placing full control in the user’s hands. Here is how they compare:
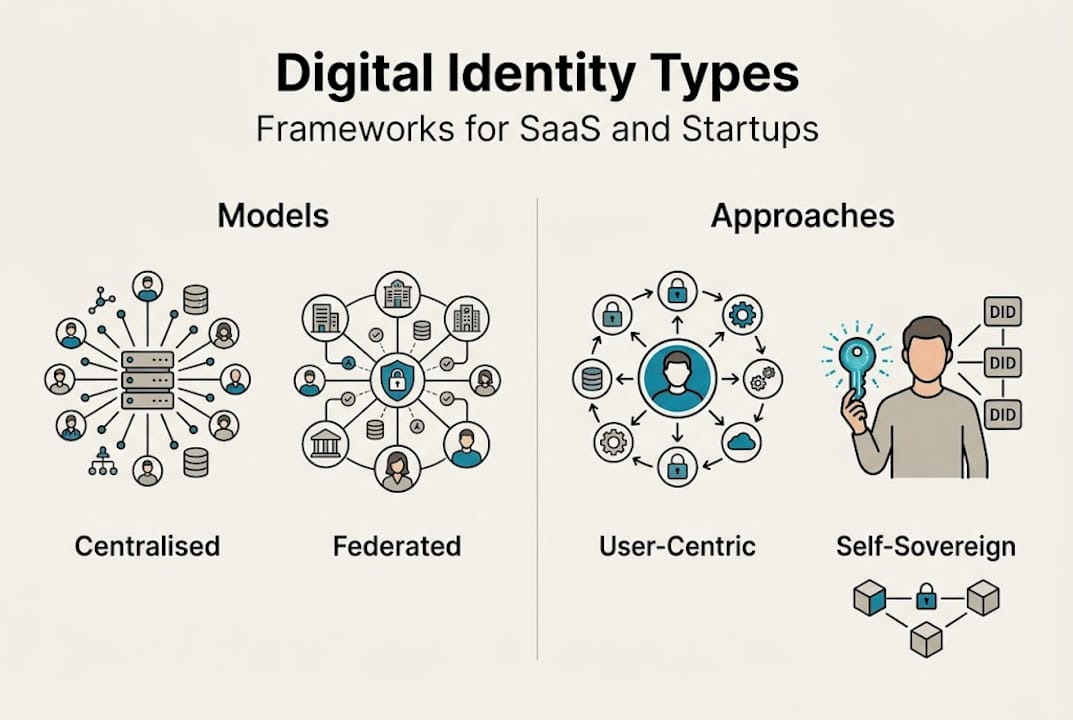
| Model | Control | Privacy | Risk | Recovery |
|---|---|---|---|---|
| Centralised | Platform | Low | High (single point) | Platform-managed |
| Federated | Shared | Medium | Distributed | Provider-dependent |
| SSI | User | High | Low (decentralised) | User-managed |
In practice, a user’s journey looks like this:
- Identity creation: The user provides attributes (name, email, documents).
- Proofing: The system verifies those attributes against trusted sources.
- Credential issuance: A credential (passkey, token, verifiable credential) is issued.
- Authentication: On each login, the credential is checked against the stored record.
- Authorisation: The system grants access based on the verified identity and assigned permissions.
For privacy-focused SaaS and ethical startups, SSI is particularly relevant. It uses digital wallets and decentralised identifiers to let users share only what is necessary, reducing your data liability and building genuine trust with your audience. Reviewing your digital marketing workflow alongside your identity architecture ensures both systems reinforce each other.
Pro Tip: A hybrid approach combining federated identity for accessibility with SSI for sensitive data gives you the best of both worlds. Users get convenience; you get reduced liability.
Risk, resilience, and edge cases in digital identity
Understanding the systems is only half the battle. Successful brands must also anticipate and address the unique risks digital identity can bring. Edge cases include synthetic identity fraud, deepfakes in biometrics, device loss, and exclusion of vulnerable groups. Each of these can cause serious damage if you have not planned for them.
| Risk | Likelihood | Mitigation |
|---|---|---|
| Synthetic identity fraud | High | Multi-layer proofing, document verification |
| Deepfake biometric attacks | Growing | Liveness detection, behavioural analytics |
| Device loss or theft | Common | Backup authentication methods, remote revocation |
| User exclusion (no formal ID) | Moderate | Alternative proofing pathways |
Best practices to reduce exposure include:
- Conduct NIST-aligned risk assessments before selecting your identity model
- Implement multi-factor authentication as a minimum standard
- Train your team on social engineering defences, not just technical controls
- Build alternative proofing pathways for users without government-issued IDs
- Test recovery flows regularly, not just at launch
“Digital identity systems that fail to account for migrant populations, stateless individuals, or those without formal documentation risk excluding the very users ethical startups aim to serve.”
Portability and recovery deserve special attention. If a user loses their device or their identity provider shuts down, can they recover access? Your market positioning strategies will suffer if users associate your brand with being locked out of their own accounts. Plan recovery from the start, not as an afterthought.
The business case: Why digital identity matters for growth and trust
With risks managed, the true value of digital identity emerges in the impact it has on your brand’s growth, reputation, and market position. The numbers are compelling. An Okta Identity Governance deployment yielded 211% ROI via efficiency gains, with one small business improving its Net Promoter Score from 22 to 41 and reducing churn by 27% through trust-focused identity practices.

The consumer side is equally clear. 68% of consumers pay more for trusted brands. Digital identity is a direct lever on that willingness to pay.
For SaaS businesses specifically, the benefits stack up:
- Compliance readiness: GDPR and eIDAS alignment becomes far simpler with a structured identity framework
- Faster onboarding: Verified users move through your funnel with less friction
- Lower fraud costs: Proofed identities reduce chargebacks and account takeovers
- Regulatory agility: As rules evolve, a well-architected identity system adapts without a rebuild
- Brand differentiation: Ethical data stewardship is a genuine market signal, not just a compliance checkbox
Reviewing digital marketing workflow tips alongside your identity strategy helps you connect the trust you build with users to the conversion rates you report to stakeholders.
Pro Tip: Frame your digital identity investment in your external communications. Position it as part of your brand’s promise of ethical data stewardship. Customers notice, and they stay longer because of it.
Adopting and evolving digital identity in your business
Armed with strategic benefits, here is how you can put digital identity theory into successful business practice and future-proof your approach.
- Evaluate your needs: Map every touchpoint where identity is verified or assumed.
- Assess your risks: Use a NIST-aligned framework to score likelihood and impact.
- Choose your model: Centralised, federated, SSI, or hybrid, based on your user base and values.
- Implement with governance: Assign ownership, document decisions, and set review cycles.
- Test thoroughly: Include edge cases, device loss scenarios, and alternative user journeys.
- Review continuously: Regulation changes. Technology changes. Your identity system must keep pace.
Business leaders should prioritise NIST-aligned risk assessments, integrate passkeys with verifiable attributes, and adopt hybrid SSI for ethical positioning. That is the direction of travel for serious operators.
There are ongoing debates around the right balance between user and platform control, blockchain dependence, and practical governance challenges. These are not resolved questions. They require your active judgement.
Common pitfalls to avoid:
- Treating identity as a one-time implementation rather than a living system
- Choosing a model based on cost alone, without assessing user risk profiles
- Failing to document your identity governance decisions for auditors
- Ignoring legacy data migration until it becomes a crisis
Explore digital identity applications that align with your current stage and growth trajectory.
Pro Tip: Plan for identity recovery and legacy data migration from day one. The cost of retrofitting these later is significantly higher than building them in at the start.
Perspective: What most guides miss about digital identity
Most guides treat digital identity as a technical problem. It is not. It is a values problem with technical consequences.
The SaaS and ethical startup space is full of founders who implement identity correctly on paper but miss the harder question: what does your identity architecture say about your relationship with your users? SSI and federated models are not just technical choices. They are signals about who you trust and how much control you are willing to hand back.
We have seen brands grow fastest when they stop treating identity as a compliance box to tick and start treating it as a differentiator. The market leaders we work with invest in brand identity services and digital identity together, because they understand that trust is not built in a marketing campaign. It is built in every interaction a user has with your system.
The uncomfortable truth is that most startups adopt the cheapest identity solution available and then wonder why churn remains stubbornly high. Ethical positioning without ethical infrastructure is just messaging. Your identity architecture is part of your brand promise whether you intend it to be or not.
Take your SaaS brand’s digital identity further
Understanding digital identity is the first step. Turning that understanding into brand authority and measurable growth is where the real work begins. At Media House Agency, we work with SaaS founders and ethical scale-ups to align their digital infrastructure with their brand positioning, ensuring that trust is built at every layer, not just in the copy.
If you are ready to move beyond theory, explore our guidance on building SaaS brand trust, review our branding and identity expertise, or discover the B2B SaaS branding benefits that come from treating identity as a growth lever. Your next stage of growth starts with the right foundations.
Frequently asked questions
What makes a digital identity truly secure?
A secure digital identity relies on robust proofing and authentication at appropriate assurance levels, combined with user-centric recovery controls. Following NIST SP 800-63 standards gives you a clear benchmark to build against.
What are the main risks with digital identity for startups?
Key risks include synthetic identity fraud, deepfake biometric attacks, lost credentials, and the accidental exclusion of users who lack formal identification documents. Planning for these early prevents costly remediation later.
How can SaaS businesses use digital identity for market growth?
Digital identity builds user trust, enables frictionless onboarding, and supports compliance, all of which improve retention. With 68% of consumers willing to pay more for trusted brands, it is a direct growth lever.
What is self-sovereign identity (SSI), and why is it important?
SSI puts users in control by using decentralised identifiers and digital wallets, enhancing privacy and reducing platform liability. For ethical, user-centric brands, it is a strong signal of genuine commitment to data stewardship.

